The Pros and Cons of Different Types of Keyless Access

Physical keys have long been the default method for securing multifamily properties, but they come with a range of downsides — from being easily copied to requiring costly rekeying after a tenant leaves.
As a result, many property managers are turning to keyless entry systems, but deciding on the best type of credential can be a challenge. Keep reading to explore the different types of keyless credentials, breaking down their pros and cons to help you determine which one suits your property’s needs best.
PIN Codes

PIN codes are a popular, simple keyless solution. Guests or residents are given a unique numeric code to enter the property, which can be easily changed or revoked without physical involvement. If your multifamily complex uses smart locks, those codes can be changed automatically when a new resident arrives or leaves.
They are perfect for multifamily units because they reduce the need for managing traditional physical keys. However, one of the potential drawbacks of PIN codes is the risk of being shared too widely (though this can be mitigated by automatically expiring codes).
One specific type of PIN is an algorithmic pin, which changes automatically based on time or other factors, making the code harder for unauthorized users to guess. These PINs can be a convenient solution for properties without consistent internet access since they do not need real-time verification to remain effective.
Algorithmic PINs are also useful for doors that require some level of security, but aren’t quite as important as the areas where people live — storage closets, garages, laundry rooms, tennis courts, pools, etc.
In one creative example, one RemoteLock customer created “kits” for vacationing guests to make s’mores next to the fire pit on the property. The kits were kept in a locked trunk with an algorithmic pin lock and restocked weekly, and guests could pay for a kit on their phone and instantly be sent a pin to open the trunk.
Pros:
- No hardware changes required between residents
- Impossible to misplace credentials
- Convenient for temporary access for tours or maintenance
Cons:
- Codes can be shared if credentials are not managed correctly
Key Fobs or Cards

Key fobs or cards are another popular option for keyless entry. These small devices are easy to carry and provide quick access at the tap of a reader. They are often used in multifamily properties or commercial spaces where regular access control is needed. Fobs and cards are also more durable than keys and less likely to be copied compared to traditional metal keys.
However, they still carry some of the same limitations—like being misplaced or stolen. Unlike physical keys, though, access can be easily revoked in a centralized system, reducing the cost and inconvenience of changing locks.
One important distinction is the difference between proximity cards and smart cards. While they look the same, proximity cards are much more simple. They carry a tiny amount of data — usually just a facility code and card number — and when they’re presented to a card reader, the controller will confirm the card number and grant the holder access. The downside is that they’re very easy to copy or fake, limiting their security.
Smart cards, on the other hand, operate on a different frequency and can carry much more data. A smart card might hold many different credentials, for example, allowing you to control a user’s access to many different doors with one card. Smart cards also hold authentication data that can’t be copied, making it impossible for unauthorized users to clone the card.
Pros:
- Quick and convenient
- Easy to revoke credentials
- Difficult or impossible to copy
Cons:
- Requires managers to physically distribute cards
- Can be misplaced
- Can be shared with unauthorized users
Mobile Credentials
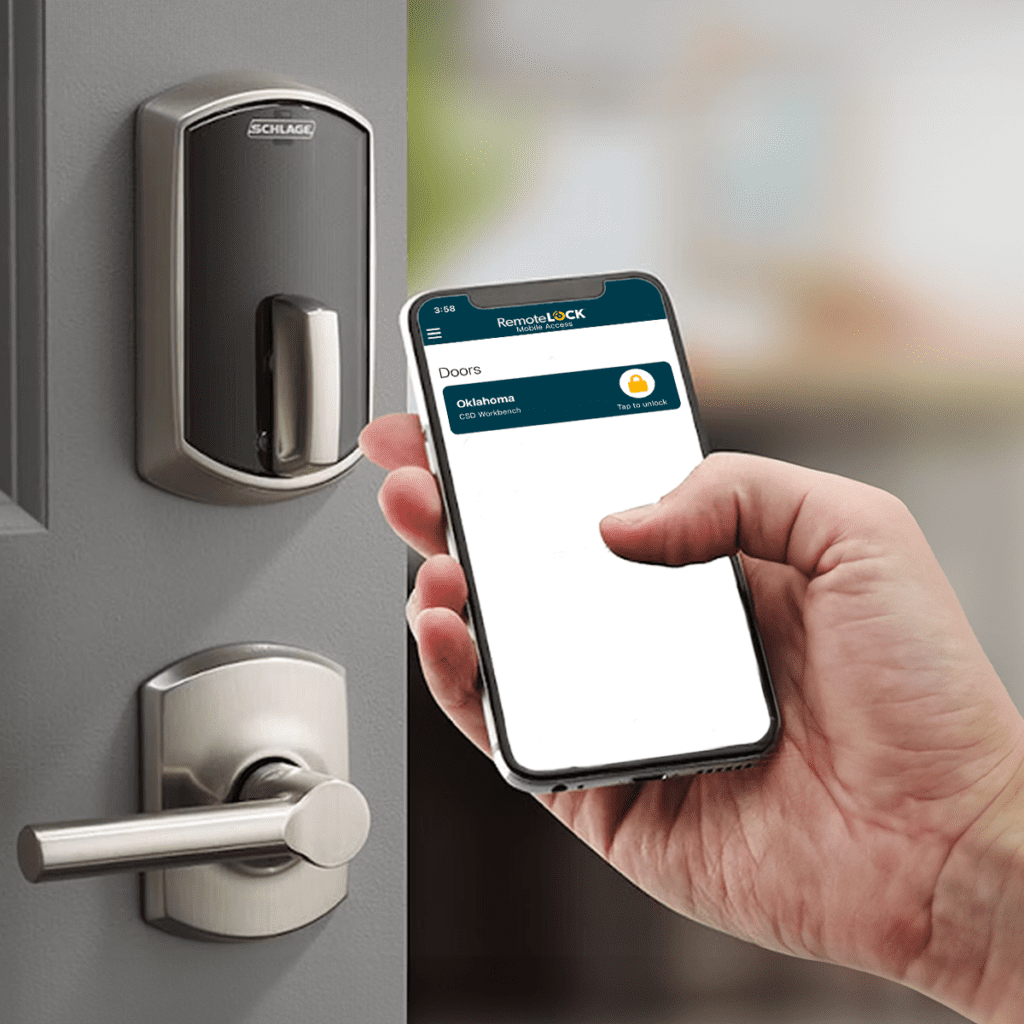
The latest in access control technology, mobile credentials offer a more high-tech solution to keyless entry by allowing residents or guests to unlock doors via their smartphones. This method provides added convenience since most people always carry their phones.
With mobile credentials, available on Schlage Control offline locks and Schlage Engage Wi-Fi smart locks, property managers can assign access remotely, grant temporary permissions, and offer a contactless experience. The primary downside is the reliance on the guest or resident having a functioning smartphone, often requiring a specific app, and there is the potential for issues with battery life or connectivity. Despite these minor drawbacks, mobile credentials are increasingly popular due to their convenience and scalability.
Pros:
- Contactless
- No need for physical credentials
- Easy to manage remotely
- Highly unlikely to be shared
Cons:
- Requires additional setup by residents
- Requires a smartphone
- Possible connectivity or battery issues
Biometric Credentials

Biometric credentials use unique physical characteristics (usually fingerprints) to provide access. These methods are considered highly secure, as they are tied to an individual and cannot be easily duplicated. However, in practical applications like vacation rentals or multifamily units, biometric credentials often prove to be less convenient.
Biometric systems require setup and enrollment for each new user, making turnovers cumbersome. Additionally, factors like moisture, dirt, or even a cut can prevent accurate readings, creating frustration for users. Despite the security benefits, the practicality of biometrics is limited.
Pros:
- High security
- Nearly impossible to duplicate
Cons:
- Inconvenient for frequent turnover
- Can be affected by environmental factors
- Complex setup
Choosing the Right Lock For You
Choosing the right lock for your multifamily property will depend on the specific needs of your property and your residents. PIN codes are easy and effective for temporary use, while mobile credentials offer unparalleled convenience and flexibility. Key fobs or cards are a sturdy, reliable choice, and biometric credentials offer top-level security at the cost of ease of use. Understanding these pros and cons will help you make an informed decision about which system works best for your property.
Interested in learning more about how RemoteLock can simplify access management for your multifamily property no matter which type of credentials you choose? Discover how our flexible solutions can enhance your property’s efficiency and security.

RemoteLock
Advanced Access Control and More
RemoteLock has been automating access control and improving on-site property operations efficiencies across multiple industries, including vacation rental and multifamily, for more than ten years. As a leading access-centered property operations software platform provider with more than 10,000 customers in 75+ countries, RemoteLock helps property managers enable, control, and automate access and climate control across their portfolio. RemoteLock’s platform saves property managers time and money through the elimination of tasks for onsite staff and helps scale businesses with greater confidence. It is differentiated by its dozens of integrations with applicable hardware and business software systems for an easy-to-use, turn-key solution.
